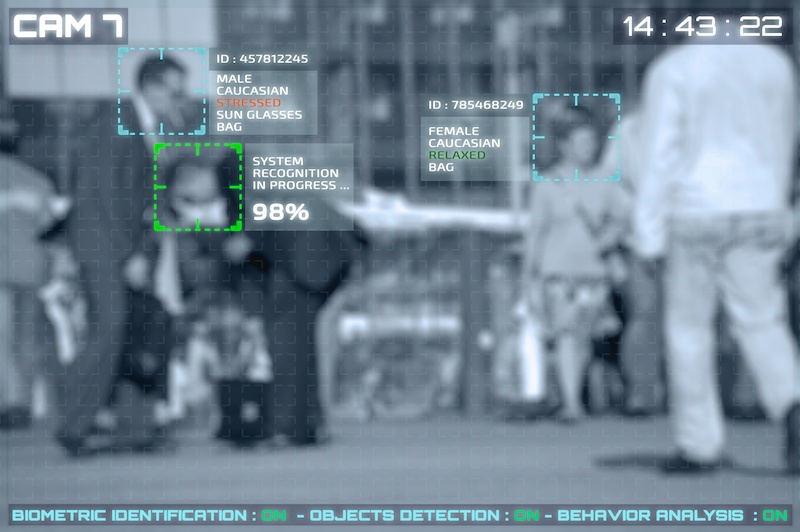
Researchers discovered the personal and biometrics data of more than a million people left publicly exposed on a database owned by Suprema, a biometric security company. Data includes facial recognition and fingerprint information collected by the UK metropolitan police, small local businesses and governments globally.
Suprema touts biometrics software called BioStar 2 that uses facial recognition and fingerprinting technology to help company administrators to control access to facilities. BioStar 2 is utilized by almost 6,000 organizations – including multinational businesses, governments, banks and the UK Metropolitan Police.
Researchers said that earlier in August, they discovered a publicly accessible ElasticSearch database totaling a hefty 23 gigabytes of data “of a highly sensitive nature.” That includes fingerprints of over one million people whose biometrics have been collected by various customers utilizing BioStar 2.
“This is a huge leak that endangers both the businesses and organizations involved, as well as their employees,” said researchers with vpnMentor in a Wednesday analysis. “Our team was able to access over 1 million fingerprint records, as well as facial recognition information. Combined with the personal details, usernames, and passwords, the potential for criminal activity and fraud is massive.”
In addition to fingerprint and facial recognition records (including images of users), also impacted was the personal data of employees such as unencrypted usernames and passwords. Within the 27.8 million records found unprotected in the database, researchers were able to seamlessly view sensitive data like employee home address and emails, employee records and security levels and more.
If bad actors were able to get their hands on this information, they could access user accounts and permissions to facilities that support BioStar 2 software, researchers warned.
Furthermore, in this specific incident, the fact that biometric data was stored plainly and not in hashed form “raises some serious concerns and is unacceptable,” Kelvin Murray, senior threat research analyst for Webroot said in an email.
“Biometrics deserve greater privacy protections than traditional credentials, they’re part of you and there’s no resetting a fingerprint or face,” he said. “Once fingerprint and facial recognition data is leaked or stolen, the victim can never undo this breach of privacy. The property that makes biometrics so effective as a means of identification is also its greatest weakness.”
The data was primarily collected from the 6,000-plus organizations that utilize BioStar 2. That includes several U.S.-based businesses, such as Union Member House, Lits Link, Phoenix Medical, and more. Also impacted was data collected by the UK metropolitan police.
It is unclear whether or not the data has been accessed by third parties other than vpnMentor; however, the database was secured eight days after it was discovered.
Biometrics Woes
The incident heightens concerns around biometric security and privacy.
Biometrics such as facial recognition is already actively used by police forces and even at the White House. And it’s not just the U.S; biometrics are spreading worldwide. The EU in April approved a massive biometrics database that combines data from law enforcement, border patrol and more for both EU and non-EU citizens.
While facial recognition has its advantages – including more efficient, faster identification – the explosion of real-world biometrics applications have privacy experts worried when it comes to certain deep-rooted privacy and security concerns.
“This is… in my opinion, worse than any of the other recent mega breaches, as it could directly relate to potential cyber terrorism attacks based on the data that has been compromised,” Matt Rose, Global Director for Application Security Strategy at Checkmarx said in an email. “The incident shines a light on organizations needing to take proper due diligence steps with the security companies they trust and contract to protect them, and more importantly, their customers’ most sensitive data.”
It’s also not the first recent biometrics security incident. In June, the U.S. Customs and Border Protection said that a recent data breach exposed photos of the faces and license plates for more than 100,000 travelers driving in and out of the country.
One of the biggest risks about biometrics security, vpnMentor researchers said, is that “facial recognition and fingerprint information cannot be changed.”
“Once they are stolen, it can’t be undone,” they said. “The unsecured manner in which BioStar 2 stores this information is worrying, considering its importance, and the fact that BioStar 2 is built by a security company.”
Disclosure Issues
Researchers first discovered the publicly accessible database on Aug. 5, and contacted the vendor on Aug. 7. The database was closed on Aug. 13, however, researchers said that the process of disclosure was messy and that Suprema was generally uncooperative through the process.
“Our team made numerous attempts to contact the company over email, to no avail,” researchers said. “Eventually, we decided to reach out to BioStar 2’s offices by phone. Again, the company was largely unresponsive.”
Suprema did not respond to a request for comment from Threatpost.
Interested in more on the internet of things (IoT)? Don’t miss our free Threatpost webinar, “IoT: Implementing Security in a 5G World.” Please join Threatpost senior editor Tara Seals and a panel of experts as they offer enterprises and other organizations insight about how to approach security for the next wave of IoT deployments, which will be enabled by the rollout of 5G networks worldwide. Click here to register.