We have read enough and more news in recent times on the surge in cyberattacks. It is crystal clear that attackers are not leaving out even the tiniest of security loopholes and are coming up with smarter ways to invade our IT network. Vulnerability management is the most crucial cyber defense process and has remained nearly the same over the last two decades. IT security teams are struggling to reduce the risk exposure and prevent cyberattacks because of the lack of this innovation. Today’s modern attack surface needs a next-gen, advanced vulnerability management approach to deal with the complex, ever-evolving attack surfaces and to curb cyberattacks.
Why Conventional Vulnerability Management is not the Best-fit for Modern Security Landscape
Advanced Vulnerability Management: What it is and How it Adds a New Spin to the Process?
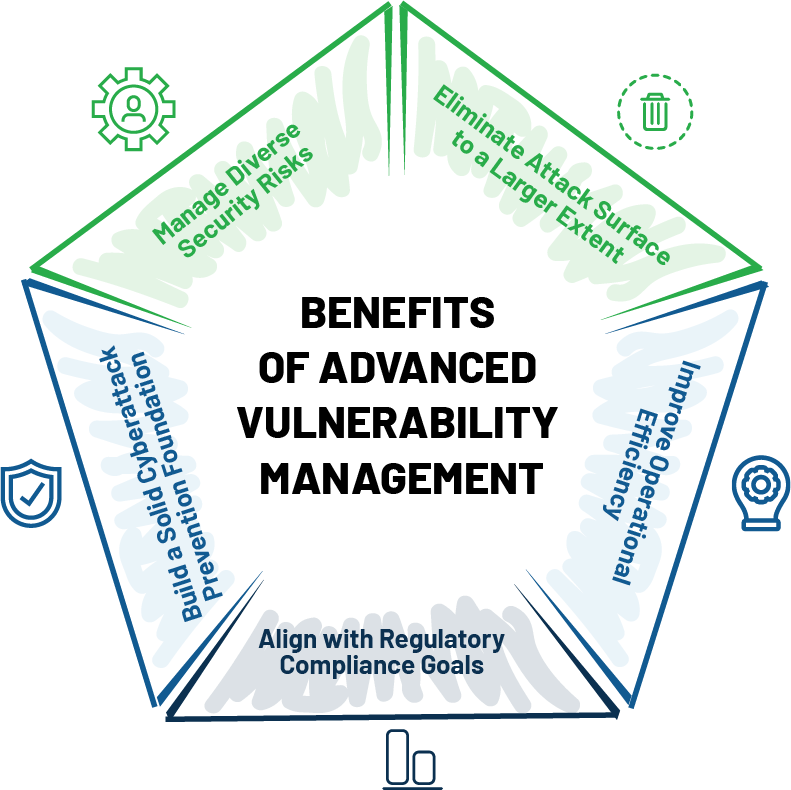
Advanced Vulnerability Management provides a broader approach to vulnerabilities and addresses different security risks in the IT vulnerability landscape. It manages a wide array of security risks, including software vulnerabilities, asset exposure, missing patches, misconfigurations, deviation in security controls, and security posture anomalies from a single place. In short, it reinvents vulnerability management, where everything right from detection to remediation of vulnerabilities is automatically performed from a centralized console.
Top Reasons to Adopt Advanced Vulnerability Management
The post-pandemic era brought numerous challenges to the digital landscape, and no doubt the attack surface has widened massively. The constant changes in the IT environment are also in favor of attackers, where IT security teams are still struggling to cope. IT security teams need to reinvent the existing vulnerability management process to deal with the rising risks and secure our dynamic IT environment. Advanced Vulnerability Management with a unified approach, integrated remediation, end-to-end automation, and a broader approach to vulnerabilities and risks will level up your vulnerability management game, enabling you to keep attacks at bay.