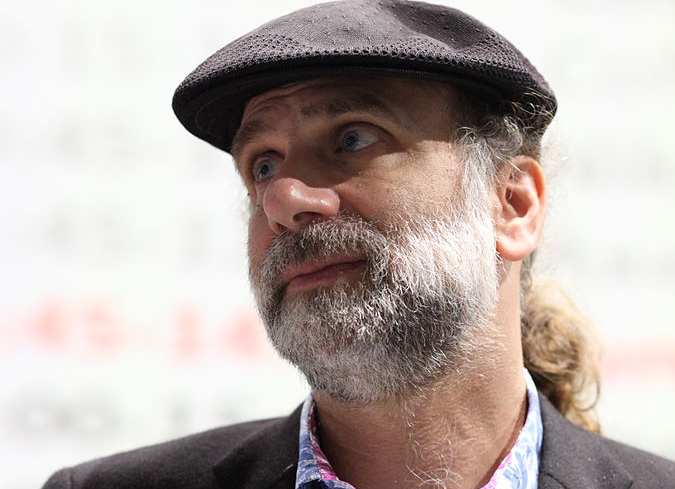
Bruce Schneier is a computer system security expert who, for decades, has been a prominent voice for cryptography and all things security. In this question-and-answer formatted interview, Schneier explains the disjunction these days’s abundance of encryption tools and a lack of individual security. Schneier also touches on a few of the risks connected with “middle ground” compromises in file encryption to placate law enforcement.TP: Exactly what does the
term”going dark “imply to you and exists a happy medium where police and cryptographers can meet?Bruce:”Going dark”is a marketing term for an FBI narrative that file encryption makes it difficult for the FBI to solve crimes. It’s propaganda, truly, and has little basis in reality. As we see again and once again, cryptography is not an impediment to police. We saw in the recent Mueller indictments(against Paul Manafort)that some of the messages sent utilizing safe and secure messaging apps were recuperated. Private investigators didn’t break the file encryption, they had the ability to discover backup copies of the message kept in numerous locations. This is not uncommon.TP: So the non-propaganda term for”going dark” would be strong file encryption,
safe interaction or safeguarding data?Bruce: What you are explaining is security. The issue with concepts of a”middle ground”is that cryptography is mathematics andlaw enforcement is policy. The laws of mathematics are not something that can be jeopardized, they simply are.TP: Today there is an abundance of encryption, or security, tools for keeping conversations and data personal. Does that mean we are more safe than we were, state five years ago?Bruce: Yes, today we have more file encryption tools than in the past. That’s primarily due to the increase of cell phones as calculating platforms, and protected messaging systems. We’ve always had protected email, however it’s never ever actually worked extremely well.Today, individuals use safe and secure messaging tools such as Signal and WhatsApp. At the exact same time, more end-user devices are natively encrypted. And more of the Web is encrypted.Are we more secure due to the fact that of this? Obviously we are, however security is a lot more than file encryption. And there is an enormous amount of insecurity in the Web services and systems we use. The risks have gotten more severe. So we are less secure than we were five years ago.TP: Less safe in that
individuals’s long tail of digital metadata can be utilized to exploit them regardless of how safe somebody’s practices are?Bruce: Partially, however I am thinking more of the increased hazard landscape. Think about something like a cars and truck. Five years ago it would be impossible to hack an automobile since theyweren’t on the internet. Now they are on the internet, and they’re vulnerable. Security utilized to be about information, and now it has to do with the real world. We’re
seeing the increase of computers that affect the world in a direct physical way, and that adds a brand-new level of risk that does not exist when we were just interested in data.TP: Are we speaking about IoT devices?Bruce: IoT belongs to it. IoT is the little things. I also worry about larger things– cyber-physical systems– such as power plants. We have actually seen effective attacks versus Ukrainian power plants and other large vital facilities. These kinds of attacks are certainly possible and becoming simpler for country states, however also non-nation state actors. More important systems are going online and that is bringing threat due to the fact that they are not vulnerable to the very same kind of threats that computers are.TP: Believing a bit more on the topic of file encryption, we are seeing a great deal of encryption cat-and-mouse games. On one hand Apple or Signal make their items more powerful to lock out 3rd parties. Then the federal government or a business security company develop a workaround. Have we ever seen this back-and-forth prior to at this pace?Bruce: It’s definitely an arms race. We have actually seen it throughout human history once again and once again. There has actually always been and always will be that arms race between opponent and defense. You can return to DES(Data File Encryption Standard)in the 1970s. There is a consistent battle between making something protected and rendering it insecure.TP: In the context of today, has the US federal government gotten much better at avoiding encryption?Bruce: It’s not just the government. Everyone has actually gotten proficient at sidestepping file encryption. The US government, foreign governments, criminals, everyone. Sidestepping file encryption is how we break systems. We almost never break the real file encryption. The Manafort indictments are a best example. Strong file encryption is tough to break. So why would you spend your time doing the tough thing when you can do the easy thing?TP: What’s your sense of the Justice Department and the FBI under Trump and where they wish to take the encryption issue?Bruce: I have no idea. Trump is a turmoil representative. Making predictions about his policies seems fruitless.TP: Believing aboutthe FBI, is there is there a middle ground in between the important things that law enforcement
wants to do and individuals’s right for security and privacy?Bruce: The middle ground is having less security and offering more access to people who wish to get into systems– that’s the FBI and the Chinese government and cybercriminals. That’s the middle ground. Consider it as a dial. Just how much security do you want to have? Just how much gain access to do you want?This notion that I can build a backdoor that just works if a [person with a] particular morality attempts to utilize it. That’s what does not work. If you’re ready to have your nuclear power plant a little less safe in exchange for giving the FBI gain access to, that’s your tradeoff. (Images courtesy of Wikimedia Commons: Rama )